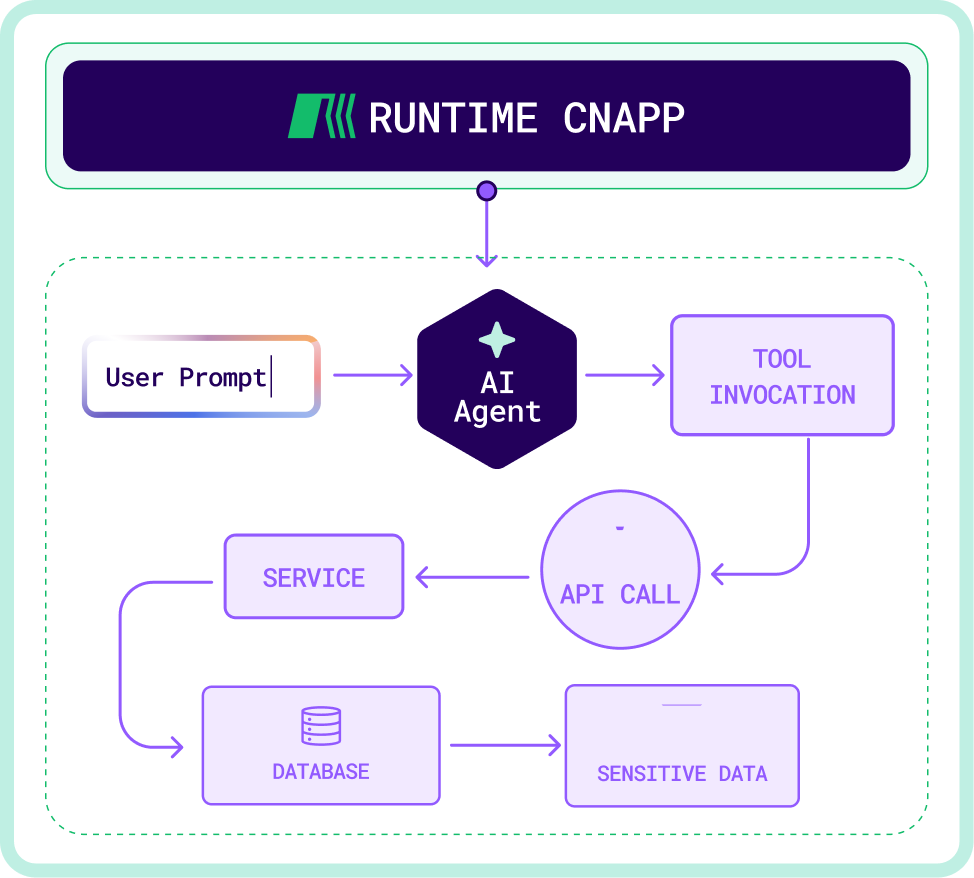
AI Security Gaps
Traditional security tools were not designed to monitor or validate this behavior.
Ensure your cloud environments remain secure in the AI era by detecting and validating AI-driven activity with runtime visibility, attack path context, and real-time detection across modern cloud environments.